The Health Insurance Portability and Accountability Act requires the healthcare industry to take measures to ensure patient privacy and data security. Understanding the regulations and staying on top of compliance is no easy task. However, both are necessary to protect patients and your business or organization. We provide an overview of HIPAA and guidance on creating a HIPAA compliance checklist to help you keep up.
Contents:
- What Is HIPAA Compliance?
- Who Must Comply With HIPAA?
- What Are the 4 HIPAA Rules?
- 1. The Security Rule
- 2. The Privacy Rule
- 3. The Breach Notification Rule
- 4. The Omnibus Final Rule
- What Are HIPAA Requirements?
- What Steps Can You Take To Ensure Compliance With HIPAA Guidelines?
- 1. Dedicate Resources
- 2. Develop Organizational HIPAA Guidelines and Procedures
- 3. Conduct Employee Training
- 4. Conduct a HIPAA Risk Assessment
- 5. Implement Plans to Address Weaknesses
- 6. Investigate HIPAA Violations and Breaches
- 7. Use a HIPAA Compliance Checklist
- What Should You Include on a HIPAA Compliance Checklist?
- Improve Compliance With HIPAA Using Fluix Document Workflows
What Is HIPAA Compliance?
HIPAA establishes a regulatory framework for securing protected health information, which includes patient health, care and financial information. Compliance ensures you meet the federal standards for medical data security and privacy.
The law applies to data in all forms. Cybersecurity is increasingly critical as the healthcare industry largely moves to online data storage and transfer. A data breach in the healthcare industry cost an average of $9.23 million in 2021, with millions of private patient records compromised. While cybercriminals use a range of tactics to infiltrate systems, compliance with HIPAA security requirements can reduce your risk.
Who Must Comply With HIPAA?
HIPAA affects any business or individual responsible for handling PHI. It also applies to anyone who may have access to sensitive data. There are three primary categories of those legally required to follow HIPAA rules:
- Covered entity: Your organization is a covered entity if it performs healthcare services that involve creating and transmitting protected health information or accepting payments for those services. Physicians, mental health professionals, dentists and health insurance providers are examples of covered entities.
- Business associate: If your business is exposed to PHI data but is not involved in creating or transmitting them, it is a business associate. Legal, tech and accounting professionals are business associates.
- Subcontractors: You have an obligation to comply with HIPAA if you are a subcontractor who performs work for a business associate that handles PHI, such as a cloud hosting provider.
Covered entities have the greatest responsibility under HIPAA rules, but any individual or business with access or exposure to sensitive data must adhere to HIPAA guidelines to protect the data.
What Are the 4 HIPAA Rules?
The regulations consist of four components, each addressing a different aspect of PHI protection. Compliance with HIPAA entails addressing all four elements in handling sensitive data.
1. The Security Rule
The prevalence of electronically stored and transmitted data necessitates specific measures to address data security. The security rule is most applicable for electronic PHI. It outlines the standards for protecting information in the following three areas:
- Premises: Standards for securing the physical locations for storing PHI, including who has access to the facilities
- Technical: Standards for securing digital storage, transmission and access for PHI
- Administrative: Standards for developing policies and procedures for managing PHI
Each measure imposes structures and procedures that restrict data access, preventing unauthorized individuals from gaining entry into the system or otherwise getting ahold of the information. To maintain compliance, your organization must address all three aspects of the security rule.
2. The Privacy Rule
The privacy rule protects patients’ rights to personal, health and financial privacy. The rule defines protected information and refers to electronic, physical and verbal communication. It also outlines documentation and patient consent requirements.
3. The Breach Notification Rule
Healthcare doesn’t exist in a bubble. Patients often see multiple providers, obtain medications from different pharmacies and pay for services using a combination of insurance and personal payment methods. Data can change hands numerous times in a single day, increasing the risk of a breach. In 2021, healthcare industry data breaches compromised PHI for 45 million patients.
HIPAA’s breach notification rule outlines specific measures companies must take when a security breach occurs. The following steps offer a framework for notifying patients and limiting the damage:
- Affected individuals’ notification plan: A written plan for how to notify individuals affected by the breach
- Public disclosure plan: Procedures for conveying information about the breach to the public
- Notification timeframe: A 60-day deadline for revealing breach investigation findings
- Secretary of Health notification: Official notification to the Secretary of Health when a breach impacts more than 500 individuals.
Cybercriminals invest resources in devising ways to circumvent security measures and take advantage of human vulnerabilities. This HIPPA component recognizes that no system is entirely unbreachable.
4. The Omnibus Final Rule
The omnibus rule broadens accountability and compliance requirements. While the regulations still bind business associates and subcontractors, covered entities also bear responsibility when a breach originates with a business associate or subcontractor. The omnibus rule also increases patients’ rights to access their own health information.
What Are HIPAA Requirements?
HIPAA requires covered entities to implement specific measures to ensure PHI security and privacy. Your organization must regularly assess its risk for breaches by identifying vulnerabilities and weaknesses. During your risk assessment, you evaluate administrative practices, IT and physical systems security and your crisis recovery plan. Once you identify your risks, you are required to devise and implement a plan for addressing them.
To ensure you meet all requirements, you must conduct an annual internal HIPAA audit. The audit protocol outlines elements of each standard for security, privacy and breach notification compliance and reflects the updated regulatory measures adopted in the Omnibus Final Rule. When your organization participates in an official HIPAA audit, you must submit the previous six years’ worth of internal audit and other relevant documentation to auditors.
What Steps Can You Take To Ensure Compliance With HIPAA Guidelines?
Maintaining compliance with HIPAA is an ongoing effort. It helps to implement procedures that your organization follows throughout the year. The following seven steps provide direction for setting up a compliance plan.
1. Dedicate Resources
Appoint or recruit responsible employees to form a HIPAA compliance team and ensure one individual leads the team. The healthcare industry is often overwhelmed with tasks and responsibilities. However, the compliance team should have time dedicated to performing HIPAA compliance tasks.
2. Develop Organizational HIPAA Guidelines and Procedures
HIPAA compliance involves adhering to the four separate rules, each with established requirements. Your organization should have well-defined policies and practices for maintaining compliance, including documentation procedures and administrative, technical and physical safeguards. You should also ensure you have a plan for handling breaches, including who is responsible for each of the plan’s components.
3. Conduct Employee Training
One of the primary reasons for security breaches is human error. All employees should be trained in HIPAA compliance requirements. Training needs to include steps for ensuring digital data security, including safe email and texting practices.
4. Conduct a HIPAA Risk Assessment
Risk assessments are an essential component of annual compliance procedures and are legally required. Your organization needs to evaluate physical, technical and administrative security. Staff training procedures and IT system security features are elements to consider during each assessment.
5. Implement Plans to Address Weaknesses
Following your risk assessment, your organization needs to address any weaknesses identified. It helps to establish a timeframe for closing the security gaps.
6. Investigate HIPAA Violations and Breaches
Not all HIPAA violations are tech breaches. It’s vital to investigate internal privacy rule violations as well as external data breaches to determine where the system broke down and why. Once you understand what went wrong, you can develop an action plan to improve policies and practices to prevent a recurrence.
7. Use a HIPAA Compliance Checklist
A checklist can help you stay on top of HIPAA compliance in your organization. The checklist should be accessible and straightforward, making it easy for your organization’s HIPAA compliance team to use.
What Should You Include on a HIPAA Compliance Checklist?
Your checklist should include sections for every compliance element, with individual tasks listed under each. The checklist should have the following areas:
- Annual HIPAA audit elements
- Gap documentation
- Remediation plans
- Staff training
- Policies and procedures
- Business associate identification
- Breach processes
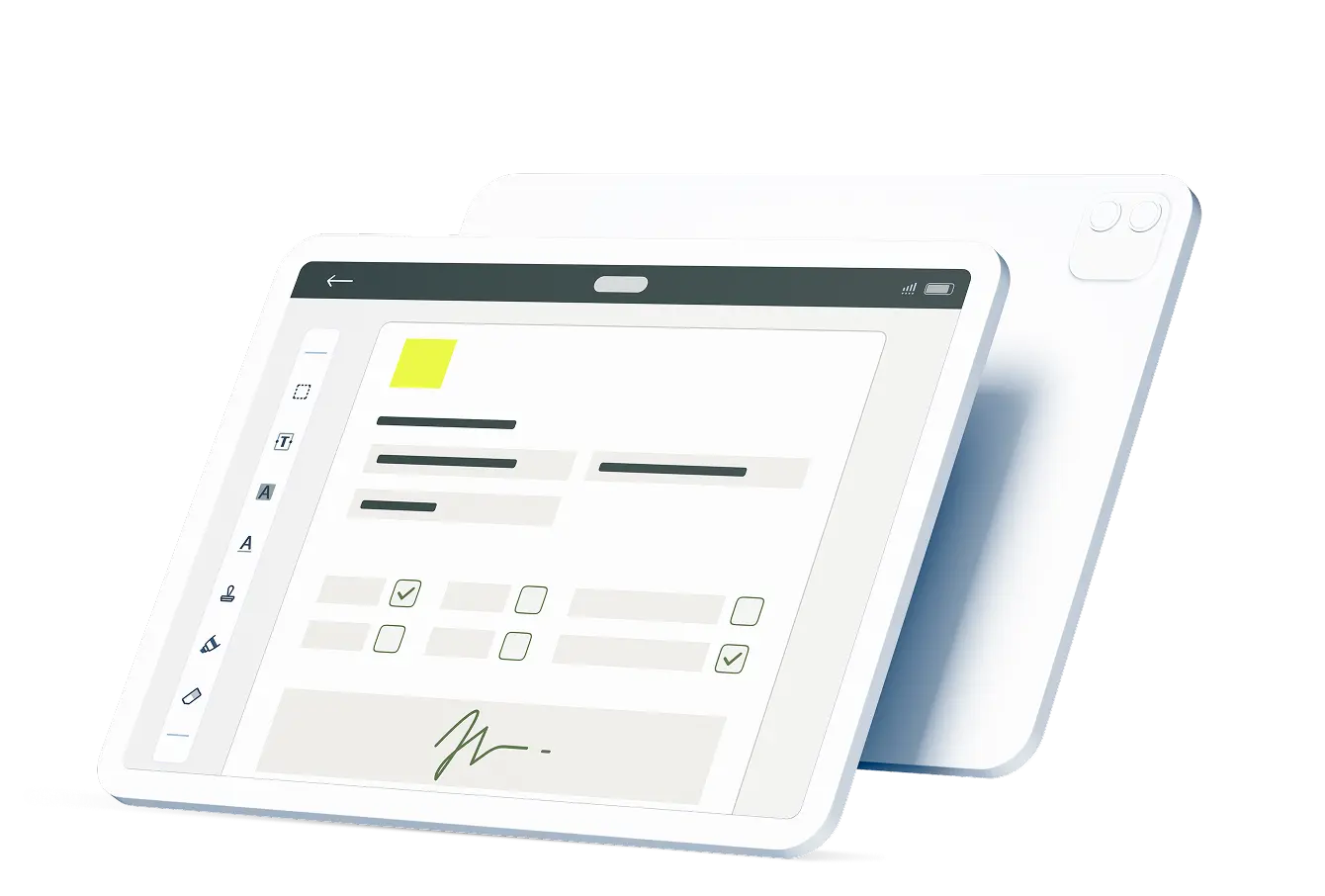
If you incorporate your HIPAA compliance checklist into your workflow management software system, your compliance team can securely access and edit it anywhere, anytime, making it easier for them to monitor progress and ensure task completion.
Improve Compliance With HIPAA Using Fluix Document Workflows
Fluix is a workflow automation system that does not require coding knowledge. It allows you to organize documentation, including your HIPAA checklist. Authorized employees can access the secure system from anywhere and on any device, increasing efficiency and improving workflow processes. Learn more about how Fluix compliance software can help you stay on top of audits and compliance.